Identity Threat Detection & Response (ITDR)
Detect and respond to identity-based threats with AI-driven monitoring and automated response across your identity infrastructure.
Overview
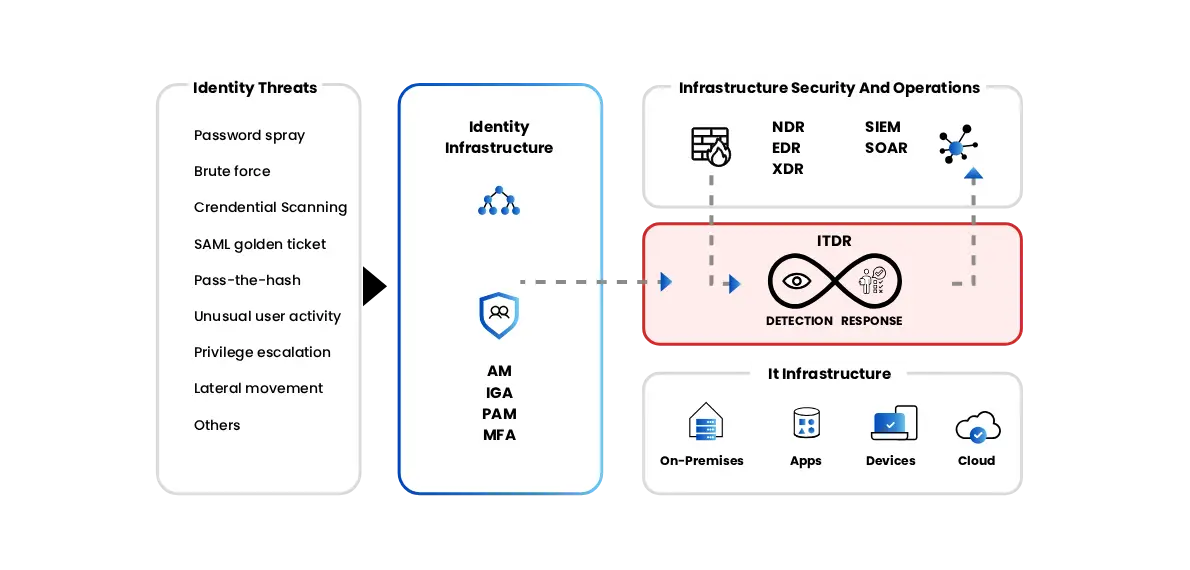
Identity-based attacks are rapidly becoming one of the most common methods used by cybercriminals to breach organizations. Compromised credentials, privilege abuse, and identity misconfigurations can lead to unauthorized access and lateral movement across enterprise systems. Corvit’s Identity Threat Detection & Response (ITDR) service, powered by StrikeReady, provides continuous monitoring of identity systems to detect suspicious activities and potential threats. By analyzing identity behavior, access patterns, and authentication events, Corvit helps organizations quickly detect, investigate, and respond to identity-related threats before they escalate.
Customer Challenge
Organizations face growing identity-based attacks as compromised credentials and privileged access misuse expose critical systems and sensitive data.
Credential Compromise
Attackers frequently steal or brute-force user credentials to gain unauthorized access to enterprise systems.
Privileged Account Abuse
Privileged accounts are often targeted by attackers to escalate access and move laterally across networks.
Limited Identity Visibility
Security teams lack centralized visibility into authentication events and identity-related activities across systems.
Slow Incident Response
Delayed detection of identity threats allows attackers to maintain persistence within the environment.
Identity-Centric Threat Protection
Identity Threat Detection
Faster Incident Response
Privileged Account Protection
Behavioral Threat Analytics
Reduced Identity Attack Surface
Automated Security Workflows
Our Solutions
Corvit Identity Threat Detection & Response uses StrikeReady’s AI-driven threat intelligence platform to detect identity-based attacks, monitor authentication activities, and enable rapid response to credential compromise incidents.
- Monitor authentication events across identity systems such as Active Directory and cloud identity platforms.
- Detect suspicious identity behaviors, credential misuse, and privilege escalation attempts.
- Automate investigation and response workflows for faster threat containment.
Identity Threat Detection
Credential Abuse Monitoring
AI-Powered Threat Intelligence
Where Identity Security Makes the Difference
Financial Services
Detect identity fraud and protect access to sensitive financial platforms.
Healthcare
Secure medical systems and prevent unauthorized access to sensitive patient records.
Government & Public Sector
Protect government systems from identity compromise and credential-based attacks.
Enterprise IT Environments
Monitor employee access across corporate systems, cloud platforms, and internal applications.
Why Choose Corvit Identity Threat Detection & Response
AI-Powered Threat Intelligence
StrikeReady’s AI-driven platform detects identity threats and correlates security events for faster investigation.
Identity Behavior Analytics
Analyze user behavior and authentication patterns to identify anomalies and suspicious activity
Integrated Security Visibility
Gain centralized visibility into identity-related activities across endpoints, networks, and cloud platforms.
Expert Security Monitoring
Corvit security experts monitor identity threats and respond quickly to protect enterprise systems.
Want more?
Enhance identity and infrastructure protection with Corvit’s advanced managed cybersecurity services.
Privileged Access Management (PAM)
Control, monitor, and secure privileged accounts across critical enterprise systems.
Zero Trust (SASE/SSE)
Implement identity-based access controls to protect applications and network resources.
Cyber Defense Center (SOC)
24/7 monitoring, threat detection, and incident response across enterprise environments.
AI-Enhanced Email Security
Prevent phishing attacks and credential theft through advanced email threat detection.
Cloud Security (CNAPP/CSPM)
Protect cloud infrastructure, workloads, and configurations from cyber threats.
Data Loss Prevention (DLP)
Prevent sensitive data leakage across endpoints, networks, and cloud platforms.
Digital Forensics & Incident Response (DFIR)
Investigate security incidents and quickly remediate breaches.
Head Office
Office # 201-204, Building No. 11, Barwaa Commercial Avenue, Doha, Qatar.
Let's Talk
Phone # +974 4000 6999
Mobile # +974 3322 8854
Email Support

Office Hours
Monday – Saturday
9:00 am – 6:00 pm
Let's Talk About Your Business Security Strategy
Have a question or need more information? Get in touch, and our cybersecurity experts will assist you.

