Zero Trust (SASE/SSE)
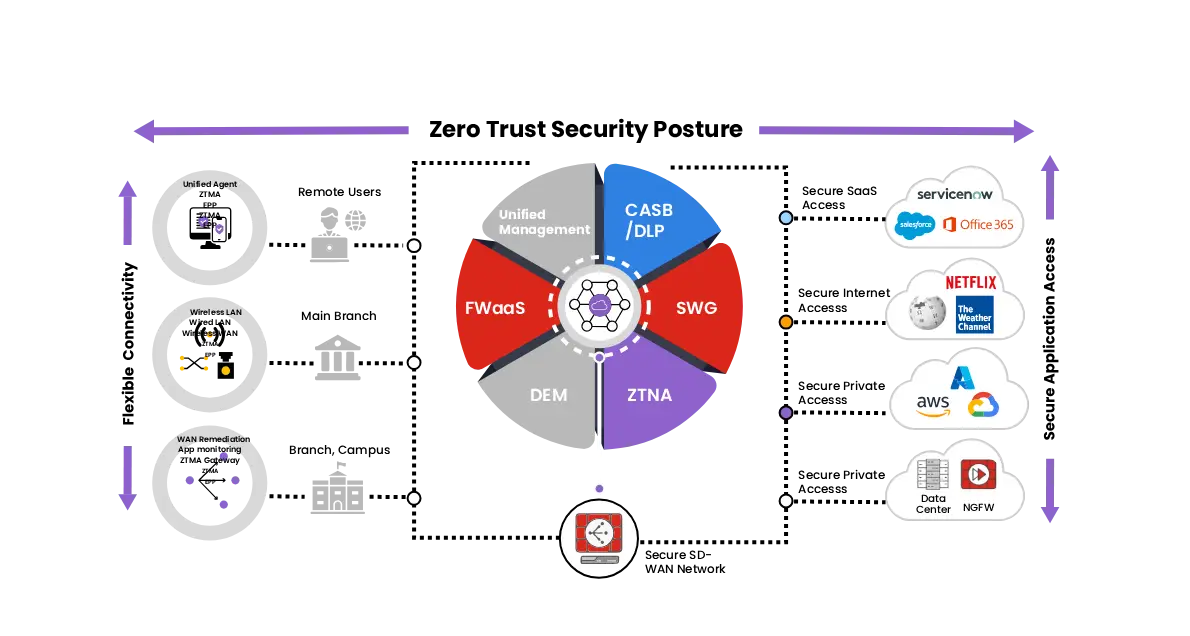
Secure user access to applications and data using Zero Trust architecture and cloud-delivered security.
Overview
Modern organizations operate in hybrid environments where employees access applications from remote locations, branch offices, and cloud platforms. Traditional network security models that rely on perimeter-based protection are no longer sufficient. Corvit’s Zero Trust (SASE/SSE) service ensures that every user, device, and connection is continuously verified before access is granted. By combining identity-based access control, secure connectivity, and cloud-delivered security services, Corvit enables organizations to protect applications, reduce attack surfaces, and securely support modern digital workplaces.
Customer Challenge
Traditional network security models struggle to protect distributed users, cloud applications, and remote access environments.
Expanding Remote Workforce
Employees accessing applications remotely increase exposure to unauthorized access and security risks.
Weak Perimeter-Based Security
Legacy security models relying on network perimeters cannot protect cloud-based applications and remote users.
Identity & Access Risks
Compromised credentials may allow attackers to access corporate applications and sensitive systems.
Complex Security Infrastructure
Managing multiple disconnected security solutions increases operational complexity and security gaps.
Identity-Centric Security
Zero Trust Access Control
Secure Remote Access
Reduced Attack Surface
Cloud-Delivered Security
Improved User Experience
Simplified Security Architecture

Our Solutions
Corvit Zero Trust (SASE/SSE) delivers secure user access to applications through identity-based authentication, secure connectivity, and cloud-delivered security enforcement.
- Implement Zero Trust access controls to verify user identity, device posture, and access permissions.
- Secure remote access to corporate applications without exposing internal networks.
- Enforce security policies across users, devices, and cloud services.
Zero Trust Access Control
Secure Access Service Edge (SASE) Architecture
Identity-Based Security Policies
Where Zero Trust Makes the Difference
Financial Services
Secure remote access for employees handling sensitive financial systems and customer data.
Healthcare
Protect access to healthcare applications and patient records across distributed environments.
Corporate Enterprises
Secure remote workforce access to cloud applications and internal business systems.
Government & Public Sector
Protect sensitive government applications with strict identity-based access controls.
Why Choose Corvit Zero Trust
Modern Security Architecture
Adopt Zero Trust principles designed for hybrid work environments and cloud-based infrastructure.
Identity-Centric Protection
Ensure access to applications is granted only after verifying user identity and device posture.
Integrated Security Services
Combine multiple security capabilities into a unified cloud-delivered security platform.
Expert Implementation & Management
Corvit cybersecurity experts design and manage Zero Trust environments aligned with organizational security needs.
Want more?
Enhance your enterprise security with Corvit’s advanced managed cybersecurity services.
Privileged Access Management (PAM)
Secure administrative accounts and control privileged access across critical systems.
Secure SD-WAN
Optimize branch connectivity while ensuring secure and reliable network communications.
Secure Web Gateway
Protect users from malicious websites and unsafe internet traffic.
AI-Enhanced Email Security
Prevent phishing attacks and malware from compromising corporate email systems.
Data Loss Prevention (DLP)
Prevent sensitive data leaks across endpoints, networks, and cloud applications
Cyber Defense Center (SOC)
24/7 monitoring, threat detection, and incident response across enterprise environments.
Dark Web Monitoring
Detect exposed credentials and sensitive data leaked across underground cyber communities.
Head Office
Office # 201-204, Building No. 11, Barwaa Commercial Avenue, Doha, Qatar.
Let's Talk
Phone # +974 4000 6999
Mobile # +974 3322 8854
Email Support

Office Hours
Monday – Saturday
9:00 am – 6:00 pm
Let's Talk About Your Business Security Strategy
Have a question or need more information? Get in touch, and our cybersecurity experts will assist you.

